The Dark Web is the part of the internet that one accesses using a particular tool. It is different from the normal web directories and stretches beyond any rules and regulations or censorship.
Explore the hidden realm of the internet with our list of the top legitimate dark websites. Dive into the secret worlds of the dark web, learn what it is, and what’s the difference between the dark web and the deep web. Also, explore the reasons why people visit these onion sites. Some sites like Reddit.com help people to interact and share content, while others are purely for entertainment.
Best Dark Web Sites: Quick List
Short on time? Have a look at the list of top legal dark web sites:
- DuckDuckGo: A privacy-focused search engine for users.
- ProPublica: The investigative journalistic ninjas defending transparency, the truth.
- Facebook Onion Site: A secret Facebook place on the Tor network.
- Reddit (Onion Site): Browse and participate in discussions anonymously.
- SecureDrop: Whistleblowers can use it as a shield to speak truth to power.
- BBC Tor Mirror: An intriguing addition to your news, the alternate reality BBC is available via the shadowy Tor network.
- ProtonMail: The encrypted email fortress where your correspondence is completely private and secure.
- The CIA: Known for their intelligence work, they also have a knack for humor.
- Tutanota: An end-to-end encrypted email service with a Tor-accessible version.
- OnionShare: Allows you to share files securely and anonymously.
- The New York Times (Onion Site): The official Tor version of The New York Times news website.
- OFTC IRC: A safe chatting network for individuals.
- Ricochet Refresh: Runs entirely over Tor. It enables anonymous, peer-to-peer conversations.
- Deutsche Welle (DW): Provides a secure access to global news.
- The Intercept: An investigative journalism platform with a Tor site for anonymous access to independent reporting.
How to Use a VPN with Tor: Quick Guide

A VPN helps you stay anonymous. Here’s how you can be safe with a VPN when accessing the dark web:
- Select a reputable VPN service provider. ExtremeVPN offers lightning-fast speeds, impenetrable security, and an expansive server network, which makes it the best option.
- Download the VPN software on your router or device and install it.
- Launch the app, then select a server of your choice.
- Start accessing onion websites anonymously.
Caution: Prioritize Safety When Visiting Dark Web Sites

There are important measures you should take to ensure your security when exploring the dark web. For example, you must use an anonymous browsing software such as Tor, a VPN, and an antivirus. The onion browser Tor provides an extra layer of security using its nodes. The VPN encrypts your internet connection, keeping your identity hidden. And the antivirus is capable of blocking virus attacks. You also have to be careful not to share your private information.
One should also remember that higher authorities can supervise the activities taking place on the dark web. For this reason, visiting some of the sites on the dark web may result in being held criminally responsible for the acts carried out within them.
Top Dark Web Websites: Detailed List

1. DuckDuckGo
Link: https://3g2upl4pq6kufc4m.onion
DuckDuckGo is a search engine designed to protect online privacy of users. It’s the company’s flagship product and its official name is Duck Duck Go Inc, which was inspired from the classic kids’ game Duck, Duck, Goose. The search engine has released extensions for external web browsers.

The DuckDuckGo website doesn’t store information, track users, or save user IP addresses. It also doesn’t keep track of the websites or search histories that its users have visited. The platform doesn’t connect any terms with users; it only keeps track of aggregate search terms.
2. ProPublica
Link: https://p53lf57qovyuvwsc6xnrppyply3vtqm7l6pcobkmyqsiofyeznfu5uqd.onion/
ProPublica does investigative journalism. In 2016, the site won the Pulitzer Prize for analyzing a story on sexual abuse cases.

To reach ProPublica, one uses a normal internet interface called cleanNet. cleanNet makes sure its site is available on the Tor network for those willing to use it. Tor browser helps to bypass country bans and enhance security and anonymity. ProPublica is among the best-designed websites you can find on the dark web.
3. Facebook Onion Site
Link: https://www.facebookcorewwwi.onion/
There are many unexpected websites on the dark web, and the Facebook Onion site is one of them. While we advise against using Facebook if you wish to maintain your anonymity, it’s interesting to see how prevalent this social media platform is ever since it joined the dark web in 2014.
This website is a replica of the actual Facebook. You can create a Facebook profile on the dark web by using an alternate username and email address, just like you do on the original platform.
However, identity verification may be impossible since Facebook is known for collecting personal data. Some people use it as a workaround for government censorship in certain nations. With Facebook’s dark web version, users can try to remain anonymous while speaking freely.
4. Reddit
Link: https://www.reddittorjg6rue252oqsxryoxengawnmo46qy4kyii5wtqnwfj4ooad.onion
Reddit has an official Tor-accessible version over the dark web. It is a social media discussion platform that is primarily a surface website. However, it maintains an onion site which allows users in restricted regions or those seeking enhanced privacy to browse and participate anonymously.
This Tor mirror has the same content and communities as the regular site, from subreddits about hobbies and news to technology, sports and science discussions. But with the added security of encrypted Tor connections.
5. SecureDrop
Link: http://sdolvtfhatvsysc6l34d65ymdwxcujausv7k5jk4cy5ttzhjoi6fzvyd.onion/
The dark web is one of the few places whistleblowers can share information, knowing they won’t be followed. The website, SecureDrop connects Journalists and whistleblowers.
Several significant newspapers and publishers have created unique SecureDrop URLs after realizing the potential of anonymous leakers on the dark web.

Additionally, SecureDrop significantly reduces the possibility of an initial metadata trail from communications with journalistic sources. Furthermore, it aims to offer a more secure medium for those exchanges than the potentially vulnerable regular corporate news networks.
6. BBC Tor Mirror
Link: http://bbcnewsv2vjtpsuy.onion/
Some governments and nations enforce strict internet censorship to prevent people from reading foreign news sources. The BBC website is one of the best examples of a news source that is unavailable in some repressive nations.
The news website of the BBC has been mirrored on the dark web by a dedicated Tor mirror. The intention is to provide an unrestricted, anonymous means for anyone, anywhere in the world, to visit the BBC website.
7. ProtonMail
Link: https://protonirockerxow.onion/
Proton Mail, a Swiss encrypted service, is one of the best onion sites and email clients. They don’t keep any logs and employ end-to-end encryption. Furthermore, the website doesn’t asks for your personal information when creating an account on it.

According to Proton, there are security benefits when utilizing Tor to access Proton Mail’s dark web version. It is more difficult for outside parties to view the sites and mail services you visit using the Tor browser. Furthermore, Tor can work around a country’s blocking of ProtonMail.
8. The CIA
Link: http://ciadotgov4sjwlzihbbgxnqg3xiyrg7so2r2o3lt5wz5ypk4sxyjstad.onion/
For those who wish to interact with the CIA anonymously, the agency has opened a shop on Tor. Everything on the main website will be accessible, including job postings, CIA contact details, and historical data such as the World Factbook. The primary distinction is that you can contact the agency without worrying about being followed.
We advise getting additional protection if you can’t bear the thought of being identified or if the data you share is compromised. For even greater anonymity when exploring the dark web, consider using a high-quality VPN. Additionally, this will add another level of data encryption, enabling secure communication with organizations like the CIA.
9. Tutanota
Link: http://tutanota7fsoctwj.onion
Tutanota is a secure, end-to-end encrypted email service that is designed for protecting user privacy. To add an extra layer of anonymity and security, it offers an official Tor-accessible .onion site. This allows users to access their email safely from the dark web.
Unlike a static onion address, Tutanota’s .onion link rotates periodically to reduce long-term exposure and protect against potential attacks.
10. OnionShare
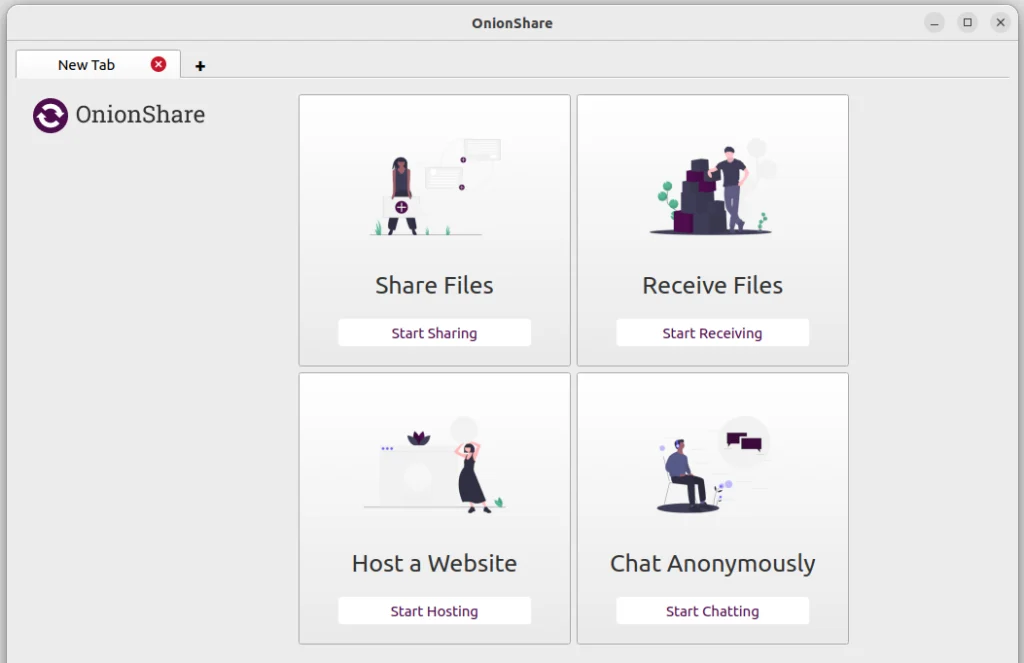
Link: http://lldan5gahapx5k7iafb3s4ikijc4ni7gx5iywdflkba5y2ezyg6sjgyd.onion/
OnionShare is an open-source tool that allows you to access files, share, host websites, or chat anonymously over the dark web. To make the process of sharing files smooth, it creates several random .onion addresses.
All the files are shared without any involvement of third parties, making it safe for private file transfers.
11. The New York Times

Link: https://www.nytimesn7cgmftshazwhfgzm37qxb44r64ytbb2dj3x62d2lljsciiyd.onion/
This onion website allows readers to access news safely and anonymously with the help of a Tor network. The site was created especially for users who are blocked from accessing the official New York Times website.
The New York Times’ onion service is completely legal and exists to support press freedom and secure access to journalism.
12. OFTC IRC
Link: irc://oftcnet6xg6roj6d7id4y4cu6dchysacqj2ldgea73qzdagufflqxrid.onion/
OFTC, abbreviated as Open and Free Technology Community, is a dedicated network created for communication among individuals and communities. It works primarily as a standard network, but some of its services are accessible via the Tor browser.
Due to its anonymous nature, it makes a great choice for privacy-focused users, activists and other individuals who want to discuss topics with ease of mind without revealing their IP address.
OFTC is a long-standing and legal chat network. Unlike most dark websites, it does not host illegal content; its focus is purely on open communication and community collaboration.
13. Ricochet Refresh
Link: http://ricochetxyz.onion
Ricochet Refresh isn’t accessible through a standard web browser. It is a decentralized, peer-to-peer messaging platform designed to provide private and anonymous communication over the Tor network.
Ricochet Refresh operates differently from traditional messaging applications. It does not rely on central servers, meaning there’s no single point that can be targeted or monitored. The Tor network makes sure that messages remain encrypted, untraceable, and private.
14. Deutsche Welle (DW)

Link: https://dwnewsgngmhlplxy6o2twtfgjnrnjxbegbwqx6wnotdhkzt562tszfid.onion
It’s an official mirror site of Germany’s international news broadcaster, Deutsche Welle. The website provides news, analysis, and multimedia content in over 32 languages. The best part? Its onion site allows users in regions with heavy censorship to access its reporting safely.
The dark web version delivers the same trustworthy journalism as the surface web site, but with added protection.
15. The Intercept

Link: http://xpxduj55x2j27l2qytu2tcetykyfxbjbafin3x4i3ywddzphkbrd3jyd.onion
It’s a Tor-accessible version of the website The Intercept, which is an investigative journalism platform. The site exposes issues related to corruption, national security and wrongdoings by the government.
What are Onion Sites?

Onion sites are websites that are only available on the dark web. These sites are browsable by networks that avoid regular search engines like Google or Bing. You can’t normally surf onion sites with Chrome, Firefox, or Edge browsers. To access onion sites, you must download a special browser invented by the Tor project.
No ordinary domain names are registered within the domain name registry for onion/dark net websites. However, they are created using a cryptographic method accessible via Tor only. Through volunteer-operated nodes, it passes internet traffic throughout the world. Over 6,000 relays in this private network ensure nobody will find out where you are from.
You can also use the Tor browser to surf the regular HTTPS sites on the web. This will improve your privacy, as it provides isolation whereby no third-party tracker or ISP can reveal your identity. On the other hand, using Tor isn’t always suitable. Onion routing makes your internet very slow but provides anonymity. Therefore, we do not advise relying on Tor to carry out data-intensive tasks such as HD streaming, playing games, torrent downloads, and video calling.
What is a Dark Web, and How Does it Work?
The dark web comprises a facet of the internet that users cannot access on common search engines like Google, Yahoo, and Bing. It is a restricted network that uses a special technology and encryption called “Onion Routing.” To access it, you need a special setup, an onion router, which passes your internet traffic through several forms of relays.
Difference Between the Deep Web and the Dark Web
The internet comprises three main parts: the surface, deep, and dark web.
The Surface web is the narrowest space of the internet. Anyone and everybody can access it without any setup. It can be accessed using typical browsers or search engines. It includes sites such as Facebook, Wikipedia, online commerce sites, and YouTube, among others.
The deep web and the dark web are often misunderstood to be the same, but they aren’t. Unlike the surface web, the deep web is the part of the internet you cannot find with your everyday search engine. Access to this part of the web is protected via a password. Furthermore, logging in or from one’s specific IP address or URL is necessary to access such deep web information.
Some of the deep web sites also use unusual TLDs like .gov, .com, or .net, which normal browsing engines will fail to track down. In other situations, some sites will blatantly deter search engines from identifying their location.
Then, a part of the deep web is the dark web which is only accessible through special software and tools. Also, some people claim that the dark web requires an invitation by a person in order to access it.
The dark web is home to many illicit activities. For example, various illegal goods and services like drugs, guns, identity thefts, pirated software, malware, and other contraband can be found on the dark web marketplaces.
However, it also contains a wide assortment of genuine information and activities that people use daily. For instance, it gives the users privacy by allowing access to information not found in the open space and sharing information in secrecy and anonymously.
Though the dark web has both pros and cons, it is important to note that the risks here far surpasses than the advantages. Therefore, it means that when going for it, you need to be careful.
Tor Browser and the Dark Web: History & Connection

The dark web originally began as a tool for communication amongst governments, big corporations, hackers, and black markets. However, technologies that involved encryptions and the Tor browser allowed the public to get through to them.
In the late 90s, The US Naval Research Laboratory developed The Onion Routing (Tor) project. Today, many sites under the .onion registry operator are accessible through a network browser.
There is no privacy on the internet since it cannot be restricted only to a certain population. The armies made the first generation of Tor to cover up spies’ communications. Eventually, this framework was revised and rolled out as an SSL browser.
Tor is similar to a normal browser like Firefox, Google, and Safari. It offers the same tunneling as on other browsers but provides extra security and passes your traffic through certain random nodes before reaching its final destination. It implies that you leave no traces of your online activities and no exposure to your browser’s browsing history.
Legitimate Reasons Why People Use the Dark Web
Read on to learn why people tend to explore the dark web:

- Activists who advocate for democracy utilize the dark web to communicate in highly secure areas like China and Iran. The anonymity of the dark web gives them a medium for accessing information that can’t be easily obtained.
- Dark web proves to be helpful for people living in restrictive environments. They might not find access to social media portals such as Facebook because of government restrictions and use it to visit such sites.
- Since the dark web offers more freedom, journalists use it to shield themselves and their sources’ privacy.
- Most users searching the dark web seek anonymity due to non-observance of others’ online activity, traffic, and geographical position, among other things.
- Some individuals may not like talking openly about their medical problems. Using the dark web is how they try to get some medical advice.
Ways to Access the Dark Websites
Mozilla Firefox
It is easy to enter the dark web using Mozilla Firefox. You only need to alter its settings. Follow these simple steps:
- Open the Mozilla Browser.
- In the search bar, type “about:config” and enter.
- Here you have to find “network.dns.blockDotOnion.”
- Change the settings to “False.”
- Restart the Mozilla browser and start surfing.
Before going into the depths of the deep web, ensure the NoScript and HTTPS Everywhere plugins are installed on your Firefox browser.
Subgraph OS
This system offers improved security as well as a high level of privacy. It is written in Tor browser code. The specifics comprise kernel hardening, application firewalling, package-level safety, filesystem encryption, meta-proxy encoding, and binary integrity.
In a nutshell, the Subgraph OS is a secure, privacy-orientated operating system that users can use in high-risk environments. You may also choose Subgraph OS as an additional alternative to Tor.
Invisible Internet Project
I2P, known as the Invisible Internet Project, is used to browse and navigate both the surface and the dark web. For example, one can access DarkWeb via I2P, which is made possible through the Tor plugin of Orchid Outproxy. A layered program runs the user’s data through it to deny access to the dark web and ensure undetectability.
Another essential security characteristic in this case is that everything entering the app from external sources, like private and public keys, is also encrypted. Its unique aspect lies in utilizing file storage that lacks any central agency through the Tahoe-LAFS plugin.
Whonix
It is also compatible with other platforms such as macOS, Linux, and Windows. Ensure your Whonix experience is similar to Tor’s, as they share the same underlying source code. There are, however, major differences within the background, despite the similarities.
Another instance is where an employee accesses Whonix’s virtual workstation machine through the internal virtual LAN. However, it can only communicate to the gateway, which is the best way for the browsers to protect user apps from getting the device’s IP.
According to the creators, despite being strong, their technique would make it impossible for any malware to detect the machine’s IP address regardless of whether it possesses root access. You should also note that Whonix is not a single browser. It is part of Whonix, an all-in-one OS that runs within a virtual machine (VM). This comprises the whole package of productivity programs such as Word software and a mail client.
The Legality of Accessing the Dark Web

Viewing and navigating the dark web is not illegal. Despite having the cons, the dark web is also used for legitimate purposes, and there are many advantages you can get from it. For example, it protects your privacy and lets you view unverifiable content and services.
Moreover, the ability to remain anonymous has made the dark web a haven for people whose existence would be compromised by using the surface web. Some of these people are whistleblowers, abuse, persecution, and activist victims, as well as politicians. Conversely, it also forms a conducive environment for crooks and other criminals who engage in illegitimate actions.
As a result, the validity of the dark web will be determined by what you do with it. Some people use it for fair purposes, while others on the dark web carry out illegal activities. Note that it is easy to find yourself in trouble when you act illegally and compromise other people’s security and liberty.
Is Using the Tor Network Legal?
No legal restrictions are associated with using anonymous browsers like Tor or I2p. They do not target the black market solely. In recent years, several individuals have utilized the Tor browser to browse the surface of the net and explore the hidden recesses within the dark web.
The anonymity of the Tor network becomes necessary due to growing online privacy concerns today. That is how one can avoid third parties monitoring their online activities. Countries that heavily censor their internet traffic will necessitate a Tor Browser or VPN for people to access the surface web.
It is important to note that even though Tor protects your privacy, you may still be charged if you engage in any criminal activity. For instance, no one should download pirated copyrighted material involved in terrorism or sharing of illegal porn. It does not mean such actions are right because you use an anonymized browser.
Dark Web Common Misconceptions
Dark web is a bit mysterious and is often misunderstood.
Here are some common misconceptions that you should know about the dark web:
- You can access it with your regular browsers.
- Everything on the dark web is free to access.
- It is only used for illegal activities.
- All the content and sites on the deep and dark web are dangerous.
- No one can track your activities on the dark web.
- Dark web is illegal to use in every country.
- It is only used by criminals and hackers.
- Only the banned and prohibited goods are sold on the dark web marketplaces.
Types of Threats Associated with the Dark Web

Is it safe to operate on the dark web? Well, it can be risky. For this reason, you should not just see the dark web as a place for general privacy. Common dark web dangers include:
Scams
A vast portion of what passes for “service” on the dark web are elaborate lies and frauds. Other services are real; if you need something, you will receive it after reaching a certain price agreement. Unfortunately, some individuals utilize the dark web’s image to scam people. Malicious hackers may use phishing to steal your data, extort you, or access other sensitive materials such as intellectual property.
Government Monitoring
Various government bodies monitor the best Tor sites around the world. Some even express concerns, for example, if this implies that law enforcement can monitor the happenings on the dark web, so to speak, as in the case of Silkroad site administrator, one of the biggest illegal marketplaces in the so-called deep space. Law enforcers can use custom software to penetrate the dark web and detect activity analysis.
Even if there is nothing wrong with what you do, you can still be watched over — very closely. Some countries regard evasion of government dictates for new political beliefs as a punishable crime. One of these is, for instance, the Great Firewall, whereby China blocks any Western website it considers harmful. Accessed information may also make you end up on a watch list or be targeted for imprisonment.
Malicious Software
The dark web can help criminals to infuse malware into your devices. Therefore, any unaware individual can get infected through the devices they use. Unlike most sites on the surface web, many .onions don’t take essential steps to give user protection.
They can expose you to botnets, ransomware, keyloggers, and phishing viruses. Therefore, by visiting dark net sites unprotected, you expose yourself to potential attacks that may target you. This danger may spread to your collection of smart devices networked on the internet.
Tor protects you when browsing the dark web, but other things about your online activity will be a trail that will give away your real identity. Therefore, you should only rely on a trusted VPN like ExtremeVPN for greater safety and anonymity.
Tips to Stay Safe When Accessing the Dark Web
If you’re trying to enter the dark web, make sure you do so safely. These tips will help you:
Separate Your Real Life from Your Online Persona
Never expose your data on the dark web. Wherever possible, develop fresh burner accounts and documents. Use prepaid and anonymous credit cards for secure transactions while buying from the dark web. Make sure to refrain from using payment methods that disclose your identity.
Trust Your Instinct
You should always be on alert while on the web and trust your gut feeling. Do not take it at face value. Most people are not what they appear to be. Also, beware of the dark web links you visit and the media you consume. Only open any site if you feel it might be correct.
Use Active Monitoring of Financial and Identity Theft
Several online facilities now provide identity security. Hence, it is compulsory to ensure that you secure the services of a trusted supplier for safety when using the dark web.
Disable Java and ActiveX in Your Network Settings
Hackers can use ActiveX or Java vulnerabilities to compromise the systems with these frameworks. Therefore, you shall turn these off in your network settings at places where you will encounter various threats that make you unsafe.
Avoid Downloading Dark Web Files
There are many types of malware infections in the dark web because it has no control. Therefore, you should only open dark web attachments if necessary and avoid downloading all the files that appear here. In addition, ensure that you run a thorough dark web scan using advanced antivirus software when downloading files.
Use a Secondary Non-admin Account
Your main account comes with admin permissions, which can pave the path for malware attacks. By using a non-admin account for everyday tasks, you can protect your system from malware that tries to penetrate admin permissions.
ExtremeVPN: The Best VPN for Dark Web Websites
ExtremeVPN is the best VPN choice for accessing Tor sites. It supports the safest and most trusted VPN protocols, including IPSec/IKEv2, WireGuard, and OpenVPN. These protocols assure you of the best P2P sharing, encryption, streaming, and speed.
Moreover, we have dedicated apps for all popular devices, including Windows, Mac, iOS, Android, and router types. It’s easy to install and requires no special configuration.

Our VPN has over 6,500 servers in 78 countries. Each of those countries is home to users of the best server to get into it. Additionally, it supports a maximum of ten devices at any given time. Users do not have to log out from one device to connect with ExtremeVPN on another.
Additionally, ExtremeVPN provides unlimited bandwidth, thus allowing users to enjoy anything without worrying about data limits. It offers users with high data transmission rates that enables them to stream, game, scroll, download, upload, and do anything without buffering or slow load times.
Also read: Tor vs. VPN: What Are the Differences?
